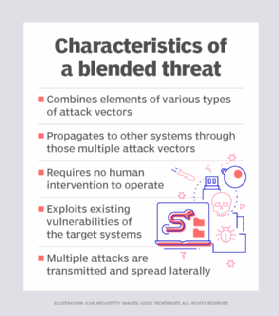
Unistal Global - What is Blended threat? To Protect yourself from any online threat download #ProtegentAntivirus - https://www.protegent360.com/antivirus.html #Protegent is world's only #Antivirus having inbuilt #datarecovery software with advanced ...
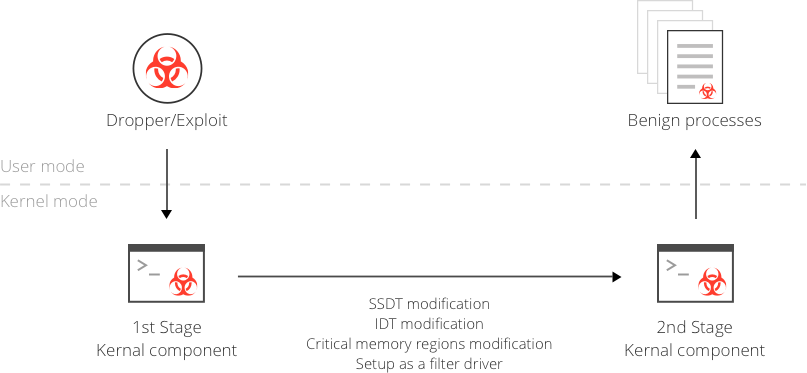
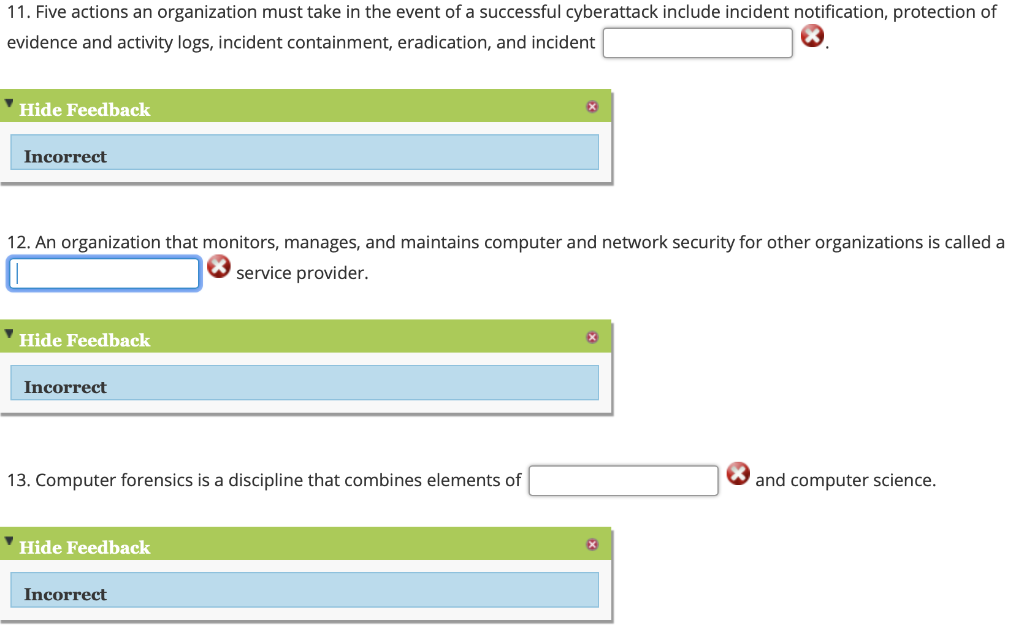
BLENDED ATTACKS EXPLOITS, VULNERABILITIES AND BUFFER-OVERFLOW TECHNIQUES IN COMPUTER VIRUSES By: Eric Chien and Peter Szor Presented by: Jesus Morales. - ppt download

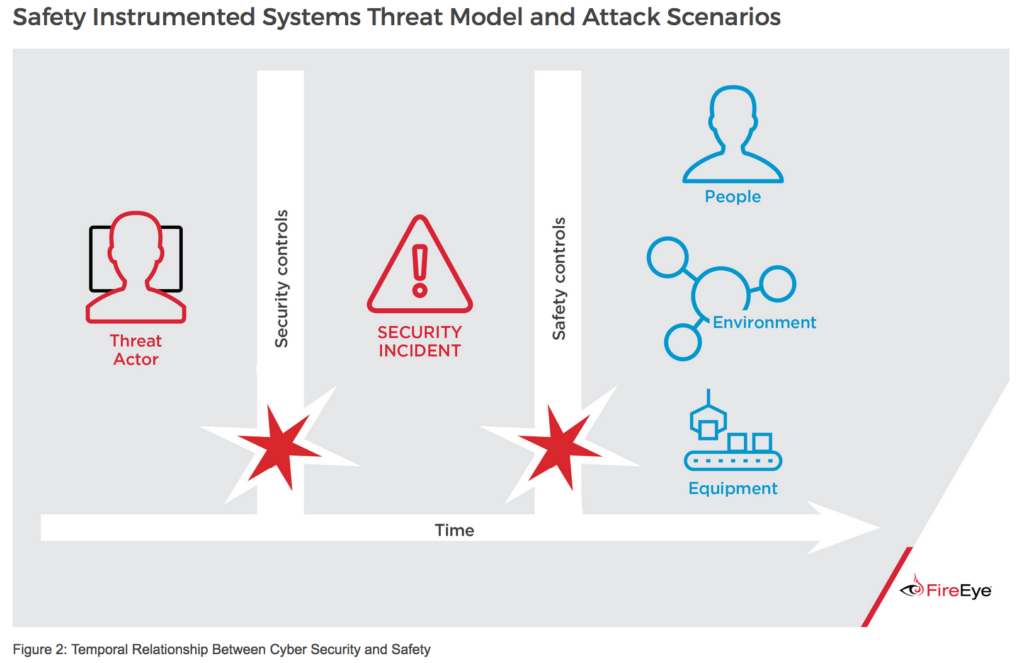
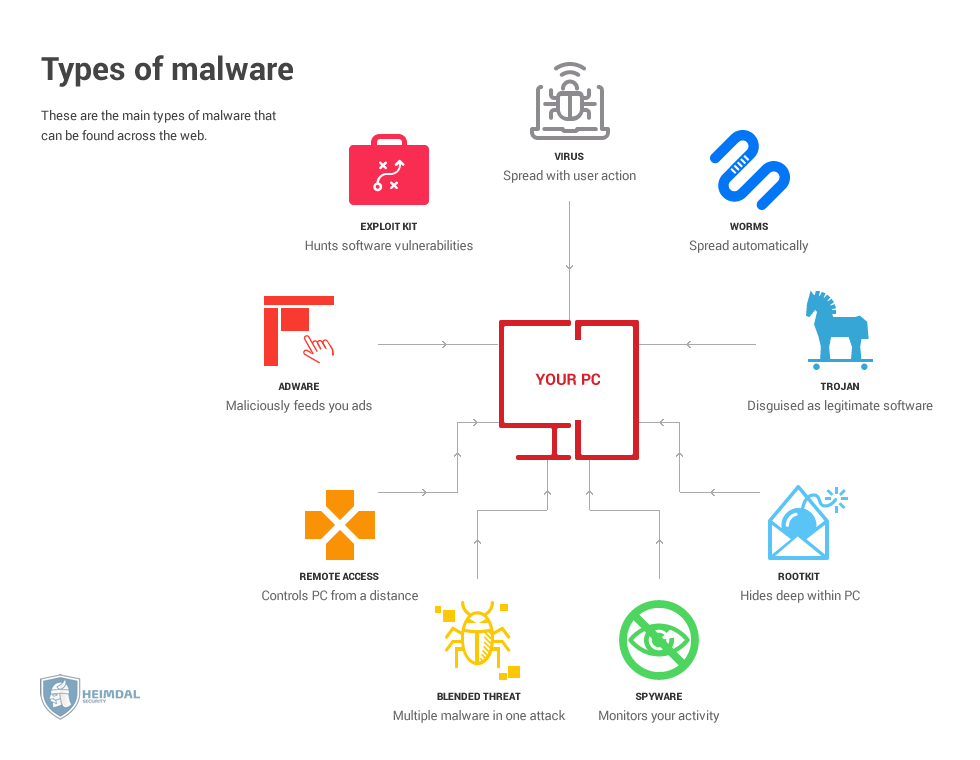
Whiz Security - Blended Threat A blended threat is an exploit that combines elements of multiple types of malware and usually employs multiple attack vectors to increase the severity of damage and

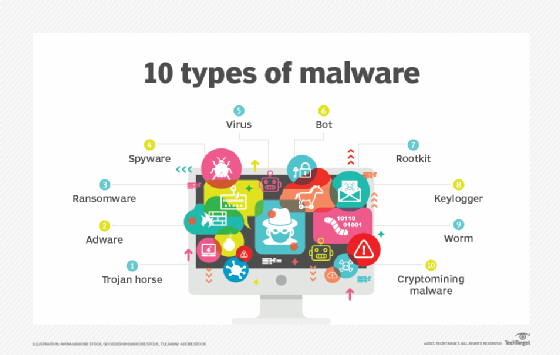
Computer Worm Computer Virus Trojan Horse Malware, PNG, 500x559px, Computer Worm, Artwork, Blended Threat, Computer, Computer